How to Generate the Phishing Report
This article will provide you with information on how to run and read the Phishing Report, so you can quickly assess how your teams are doing; who is vigilant when it comes to nefarious email and who might need a bit more education on the topic of phishing, ransomware and malware.
How to Run the Report
- Log in to the LMS, and click on the Manage drop-down menu.
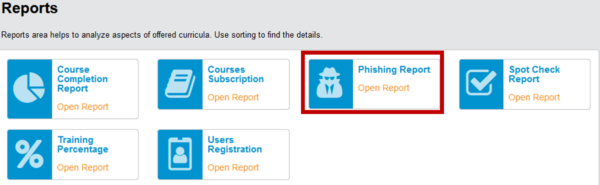
Select Reports.

- Select Phishing Report.
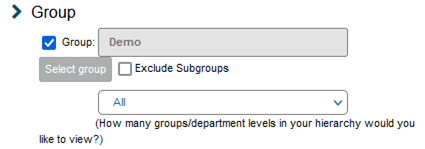
- Your property or hotel management company should be displayed.
Use the drop-down to narrow down the report to a specific location or department.
- Ensure the Status is set to Active.

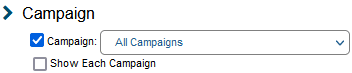
- Select the campaign you want to generate a report on.
Feel free to contact us, if you don’t know the campaign title for your property or management company.
Typically, the campaign name will be constructed as follows:
– Your HMC Name
– Type of campaign: EDU [Educational] / DEC [Deceptive]
– Ordinal number of the campaign
– Launch date: [Year, Month, Day]For example, Demo PGM Dec 3 20200807 would be your third campaign this year, launched on August 7th. This campaign was deceptive, so employees were not alerted if they failed the simulation.
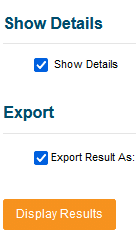
- Click Display Results to view the results.
- If you are interested in how particular users did, select Show Details. You can also export the report by choosing the desired format and clicking Display Results again.
How to Read the Report

- Group: Your property management group, or your location / property and departments will be listed based on the access you have in VENZA PEAK.
- Campaign Percentage: The overall score of the campaign based on the percentage of employees who passed the campaign.
- Email Sent: The number of emails that were sent by VENZA. This number is based on the number of your employees who have their email listed in their profile and the whitelisting of VENZA’s IP and Domains. Reach out to your Customer Success Representative to learn more about whitelisting and what is needed for a successful campaign.
- Email Open: Refers to the number of employees who open and review the phishing campaign email. Opening the phishing campaign email does not count against the user, as viewing the email is generally considered safe.

- Email Click: If an employee clicks on the link in the email, they failed the campaign.
- Data Submitted: An employee who clicks the link in the phishing campaign email is brought to our decoy site, where they are asked to submit their personal credentials (email and password). This also counts as failing the campaign.
